NEWS
Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]
-
Hi Ingo,
ich habe genau den Timeslot erwischt beim Update des iobroker.zigbee2mqtt Adapters.
Die Vorgehensweise zur Lösung eines einzelnen Adapters hat bei mir geholfen.
Erwähnenswert ist, dass der Befehl npm list @iobroker/adapter-core „empty“ anzeigte.
Danke für den Fix!!!!
Grüße, Jan
@nukleuz sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
dass der Befehl npm list @iobroker/adapter-core „empty“ anzeigte.
warst du im richtigen Verzeichnis?
-
@nukleuz sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
dass der Befehl npm list @iobroker/adapter-core „empty“ anzeigte.
warst du im richtigen Verzeichnis?
-
@nukleuz Dann hab ich noch einen

in einer früheren Version des Startposts stand ein unvollständiger Befehl, da kam tatsächlich nur eine leere Liste
-
@nukleuz Dann hab ich noch einen

in einer früheren Version des Startposts stand ein unvollständiger Befehl, da kam tatsächlich nur eine leere Liste
Ich habe in meinem Thread gelesen, dass es durch meinen Fehler doch zu Problemen kommen kann.
Siehe:
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/20
Gibt es da einen Workaround? -
Ich habe in meinem Thread gelesen, dass es durch meinen Fehler doch zu Problemen kommen kann.
Siehe:
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/20
Gibt es da einen Workaround?@muckel said in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
Ich habe in meinem Thread gelesen, dass es durch meinen Fehler doch zu Problemen kommen kann.
Siehe:
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/20
Gibt es da einen Workaround?@apollon77
Geht drum dass muckel einnpm i @iobroker/adapter-coreauf der obersten Ebene gestartet hat. Damit läuft admin zwar, aber ein explizites Install ist ja nicht "gut". Kannst du sagen ob bzw. wie das zu fixen wäre?
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/11 -
@muckel said in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
Ich habe in meinem Thread gelesen, dass es durch meinen Fehler doch zu Problemen kommen kann.
Siehe:
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/20
Gibt es da einen Workaround?@apollon77
Geht drum dass muckel einnpm i @iobroker/adapter-coreauf der obersten Ebene gestartet hat. Damit läuft admin zwar, aber ein explizites Install ist ja nicht "gut". Kannst du sagen ob bzw. wie das zu fixen wäre?
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/11@mcm57 @apollon77
Heute im log entdeckt:Nach npm audit kam folgender Vorschlag:
To address issues that do not require attention, run:
npm audit fixTo address all issues possible (including breaking changes), run:
npm audit fix --forceSome issues need review, and may require choosing
a different dependency.
Was soll ich tun?2024-04-21 04:15:05.778 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.779 - error: javascript.0 (1981571) WARN deprecated har-validator@5.1.5: this library is no longer supported 2024-04-21 04:15:05.813 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.813 - error: javascript.0 (1981571) WARN deprecated node-inspect@2.0.0: This module is part of Node.js core and does not need to be installed separately. It is now unmaintained. 2024-04-21 04:15:05.842 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.843 - error: javascript.0 (1981571) WARN deprecated uuid@3.4.0: Please upgrade to version 7 or higher. Older versions may use Math.random() in certain circumstances, which is known to be problematic. See https://v8.dev/blog/math-random for details. 2024-04-21 04:15:05.861 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.861 - error: javascript.0 (1981571) WARN deprecated request@2.88.2: request has been deprecated, see https://github.com/request/request/issues/3142 2024-04-21 04:15:07.405 - info: javascript.0 (1981571) added 98 packages, and audited 103 packages in 4s 2024-04-21 04:15:07.406 - info: javascript.0 (1981571) 4 packages are looking for funding run `npm fund` for details 2024-04-21 04:15:07.409 - info: javascript.0 (1981571) 2 moderate severity vulnerabilities Some issues need review, and may require choosing a different dependency. Run `npm audit` for details.erich@smarthome:~$ cd /opt/iobroker erich@smarthome:/opt/iobroker$ npm audit [sudo] password for erich: # npm audit report @octokit/webhooks 10.0.0 - 10.9.1 Severity: high Unauthenticated Denial of Service in the octokit/webhooks library - https://github.com/advisories/GHSA-pwfr-8pq7-x9qv fix available via `npm audit fix` node_modules/@octokit/webhooks ajv <6.12.3 Severity: moderate Prototype Pollution in Ajv - https://github.com/advisories/GHSA-v88g-cgmw-v5xw fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/node-blink-security/node_modules/ajv har-validator 3.3.0 - 5.1.0 Depends on vulnerable versions of ajv node_modules/node-blink-security/node_modules/har-validator request * Depends on vulnerable versions of har-validator Depends on vulnerable versions of hawk Depends on vulnerable versions of tough-cookie node_modules/machinepack-http/node_modules/request node_modules/node-blink-security/node_modules/request node_modules/request dropbox-v2-api * Depends on vulnerable versions of request node_modules/dropbox-v2-api iobroker.backitup >=0.3.0 Depends on vulnerable versions of dropbox-v2-api node_modules/iobroker.backitup harmonyhubws * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-native node_modules/harmonyhubws iobroker.harmony >=1.1.1 Depends on vulnerable versions of harmonyhubws node_modules/iobroker.harmony iobroker.deconz >=0.2.0 Depends on vulnerable versions of request node_modules/iobroker.deconz iobroker.hue-extended * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/iobroker.hue-extended iobroker.javascript * Depends on vulnerable versions of request node_modules/iobroker.javascript iobroker.mihome-vacuum >=2.0.7 Depends on vulnerable versions of request node_modules/iobroker.mihome-vacuum iobroker.netatmo 0.5.0 - 0.5.1 || >=1.1.7 Depends on vulnerable versions of request node_modules/iobroker.netatmo iobroker.netatmo-crawler * Depends on vulnerable versions of request node_modules/iobroker.netatmo-crawler iobroker.nuki-extended * Depends on vulnerable versions of nuki-web-api Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/iobroker.nuki-extended iobroker.rflink >=1.0.3 Depends on vulnerable versions of avrgirl-arduino Depends on vulnerable versions of request node_modules/iobroker.rflink iobroker.smartgarden >=0.5.1 Depends on vulnerable versions of request node_modules/iobroker.smartgarden iobroker.whatsapp-cmb * Depends on vulnerable versions of request node_modules/iobroker.whatsapp-cmb le-acme-core * Depends on vulnerable versions of request Depends on vulnerable versions of rsa-compat node_modules/le-acme-core iobroker.js-controller >=1.5.4 Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-adapter Depends on vulnerable versions of @iobroker/js-controller-cli Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db Depends on vulnerable versions of le-acme-core node_modules/iobroker.js-controller machinepack-http 0.2.3 - 8.0.0 Depends on vulnerable versions of request node_modules/machinepack-http bagpipes * Depends on vulnerable versions of machinepack-http node_modules/bagpipes node-blink-security * Depends on vulnerable versions of request node_modules/node-blink-security iobroker.blink4home * Depends on vulnerable versions of node-blink-security node_modules/iobroker.blink4home node-gyp <=7.1.2 Depends on vulnerable versions of request node_modules/usocket/node_modules/node-gyp usocket 0.2.2 - 0.3.0 Depends on vulnerable versions of node-gyp node_modules/usocket dbus-next * Depends on vulnerable versions of usocket Depends on vulnerable versions of xml2js node_modules/dbus-next node-ble >=0.0.2 Depends on vulnerable versions of dbus-next node_modules/node-ble iobroker.radar2 >=2.0.0 Depends on vulnerable versions of node-ble node_modules/iobroker.radar2 nuki-web-api * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/nuki-web-api request-promise >=0.0.2 Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-core Depends on vulnerable versions of tough-cookie node_modules/request-promise samsungtv Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/samsungtv iobroker.samsung >=0.5.1 Depends on vulnerable versions of samsungtv node_modules/iobroker.samsung request-promise-core * Depends on vulnerable versions of request node_modules/@cypress/request-promise/node_modules/request-promise-core node_modules/request-promise-core @cypress/request-promise * Depends on vulnerable versions of request-promise-core node_modules/@cypress/request-promise node-telegram-bot-api >=0.64.0 Depends on vulnerable versions of @cypress/request-promise node_modules/node-telegram-bot-api iobroker.telegram >=2.1.0 Depends on vulnerable versions of node-telegram-bot-api node_modules/iobroker.telegram request-promise-native >=1.0.0 Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-core Depends on vulnerable versions of tough-cookie node_modules/request-promise-native smartmeter-obis * Depends on vulnerable versions of request node_modules/smartmeter-obis iobroker.smartmeter * Depends on vulnerable versions of smartmeter-obis node_modules/iobroker.smartmeter syno * Depends on vulnerable versions of nconf Depends on vulnerable versions of request node_modules/syno iobroker.synology * Depends on vulnerable versions of syno node_modules/iobroker.synology axios <=0.27.2 || 1.0.0 - 1.5.1 Severity: high Axios vulnerable to Server-Side Request Forgery - https://github.com/advisories/GHSA-4w2v-q235-vp99 axios Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-cph5-m8f7-6c5x Axios Cross-Site Request Forgery Vulnerability - https://github.com/advisories/GHSA-wf5p-g6vw-rhxx Axios Cross-Site Request Forgery Vulnerability - https://github.com/advisories/GHSA-wf5p-g6vw-rhxx Depends on vulnerable versions of follow-redirects fix available via `npm audit fix --force` Will install iobroker.hue@0.6.0, which is a breaking change node_modules/@alcalzone/pak/node_modules/axios node_modules/iobroker.awattar/node_modules/axios node_modules/iobroker.broadlink2/node_modules/axios node_modules/iobroker.withings/node_modules/axios node_modules/node-hue-api/node_modules/axios node_modules/node-ical/node_modules/axios @alcalzone/pak 0.3.0 - 0.10.0 Depends on vulnerable versions of axios node_modules/@alcalzone/pak @iobroker/js-controller-adapter * Depends on vulnerable versions of @alcalzone/pak Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db node_modules/@iobroker/js-controller-adapter @iobroker/js-controller-common * Depends on vulnerable versions of @alcalzone/pak node_modules/@iobroker/js-controller-common @iobroker/db-base >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/js-controller-common node_modules/@iobroker/db-base @iobroker/db-objects-file >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-objects-redis node_modules/@iobroker/db-objects-file @iobroker/db-objects-jsonl >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-redis node_modules/@iobroker/db-objects-jsonl @iobroker/db-objects-redis >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base node_modules/@iobroker/db-objects-redis @iobroker/db-states-file >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-states-redis node_modules/@iobroker/db-states-file @iobroker/db-states-jsonl >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-redis node_modules/@iobroker/db-states-jsonl @iobroker/db-states-redis >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base node_modules/@iobroker/db-states-redis @iobroker/js-controller-cli * Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db node_modules/@iobroker/js-controller-cli @iobroker/js-controller-common-db * Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-common node_modules/@iobroker/js-controller-common-db iobroker.awattar >=1.0.6 Depends on vulnerable versions of axios node_modules/iobroker.awattar iobroker.broadlink2 >=2.1.0 Depends on vulnerable versions of axios node_modules/iobroker.broadlink2 iobroker.withings * Depends on vulnerable versions of axios node_modules/iobroker.withings node-hue-api 2.0.0-RC1 - 5.0.0-alpha.2 Depends on vulnerable versions of axios node_modules/node-hue-api iobroker.hue >=0.6.2 Depends on vulnerable versions of node-hue-api node_modules/iobroker.hue node-ical 0.15.3 - 0.16.1 Depends on vulnerable versions of axios node_modules/node-ical iobroker.jarvis >=3.1.3 Depends on vulnerable versions of node-ical Depends on vulnerable versions of semver node_modules/iobroker.jarvis cookiejar <2.1.4 Severity: moderate cookiejar Regular Expression Denial of Service via Cookie.parse function - https://github.com/advisories/GHSA-h452-7996-h45h fix available via `npm audit fix` node_modules/cookiejar cryptiles * Severity: critical Insufficient Entropy in cryptiles - https://github.com/advisories/GHSA-rq8g-5pc5-wrhr Depends on vulnerable versions of boom fix available via `npm audit fix` node_modules/cryptiles debug <=2.6.8 || 4.0.0 - 4.3.0 Severity: high debug Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-9vvw-cc9w-f27h Regular Expression Denial of Service in debug - https://github.com/advisories/GHSA-gxpj-cx7g-858c Regular Expression Denial of Service in debug - https://github.com/advisories/GHSA-gxpj-cx7g-858c Depends on vulnerable versions of ms fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/engine.io-client/node_modules/debug node_modules/iobroker.socketio/node_modules/debug node_modules/mdns-discovery/node_modules/debug node_modules/socket.io-client/node_modules/debug node_modules/socket.io-client/node_modules/socket.io-parser/node_modules/debug engine.io 3.4.0 - 4.0.5 Depends on vulnerable versions of debug node_modules/iobroker.socketio/node_modules/engine.io socket.io 2.2.0 - 3.0.4 Depends on vulnerable versions of debug Depends on vulnerable versions of engine.io Depends on vulnerable versions of socket.io-parser node_modules/iobroker.socketio/node_modules/socket.io iobroker.socketio 3.0.0 - 3.0.13 || 3.1.3 - 3.1.5 || 4.1.0 - 5.0.2 || 6.1.0 - 6.5.7 || >=6.6.0 Depends on vulnerable versions of socket.io node_modules/iobroker.socketio iobroker.web 4.2.1 - 4.3.0 || >=5.2.3 Depends on vulnerable versions of iobroker.socketio node_modules/iobroker.web engine.io-client <=3.1.1 Depends on vulnerable versions of debug Depends on vulnerable versions of parsejson node_modules/engine.io-client socket.io-client 1.0.0-pre - 2.1.1 Depends on vulnerable versions of debug Depends on vulnerable versions of engine.io-client Depends on vulnerable versions of socket.io-parser node_modules/socket.io-client iobroker.cloud <=2.4.6 || 2.8.0 - 3.0.2 || >=4.0.11 Depends on vulnerable versions of socket.io-client node_modules/iobroker.cloud mdns-discovery >=0.1.1 Depends on vulnerable versions of debug node_modules/mdns-discovery iobroker.discovery >=0.4.4 Depends on vulnerable versions of mdns-discovery node_modules/iobroker.discovery iobroker.firetv >=0.0.3 Depends on vulnerable versions of adbkit Depends on vulnerable versions of mdns-discovery node_modules/iobroker.firetv iobroker.mydlink >=1.0.0 Depends on vulnerable versions of mdns-discovery node_modules/iobroker.mydlink socket.io-parser <=3.3.2 || 3.4.0 - 4.0.2 Depends on vulnerable versions of debug Depends on vulnerable versions of debug node_modules/iobroker.socketio/node_modules/socket.io-parser node_modules/socket.io-client/node_modules/socket.io-parser deep-extend <0.5.1 Severity: critical Prototype Pollution in deep-extend - https://github.com/advisories/GHSA-hr2v-3952-633q fix available via `npm audit fix` node_modules/deref/node_modules/deep-extend deref 0.6.0 - 0.7.2 Depends on vulnerable versions of deep-extend node_modules/deref json-schema-faker 0.2.2 - 0.4.4 Depends on vulnerable versions of deref node_modules/json-schema-faker sway * Depends on vulnerable versions of json-schema-faker Depends on vulnerable versions of z-schema node_modules/sway dicer * Severity: high Crash in HeaderParser in dicer - https://github.com/advisories/GHSA-wm7h-9275-46v2 No fix available node_modules/dicer busboy <=0.3.1 Depends on vulnerable versions of dicer node_modules/multer/node_modules/busboy multer <=2.0.0-rc.3 Depends on vulnerable versions of busboy node_modules/multer swagger-node-runner-fork * Depends on vulnerable versions of bagpipes Depends on vulnerable versions of multer Depends on vulnerable versions of sway node_modules/swagger-node-runner-fork iobroker.rest-api * Depends on vulnerable versions of swagger-node-runner-fork node_modules/iobroker.rest-api follow-redirects <=1.15.5 Severity: high Exposure of Sensitive Information to an Unauthorized Actor in follow-redirects - https://github.com/advisories/GHSA-pw2r-vq6v-hr8c Exposure of sensitive information in follow-redirects - https://github.com/advisories/GHSA-74fj-2j2h-c42q Follow Redirects improperly handles URLs in the url.parse() function - https://github.com/advisories/GHSA-jchw-25xp-jwwc follow-redirects' Proxy-Authorization header kept across hosts - https://github.com/advisories/GHSA-cxjh-pqwp-8mfp fix available via `npm audit fix --force` Will install iobroker.hue@0.6.0, which is a breaking change node_modules/iobroker.broadlink2/node_modules/follow-redirects get-func-name <2.0.1 Severity: high Chaijs/get-func-name vulnerable to ReDoS - https://github.com/advisories/GHSA-4q6p-r6v2-jvc5 fix available via `npm audit fix` node_modules/get-func-name hawk <=9.0.0 Severity: high Uncontrolled Resource Consumption in Hawk - https://github.com/advisories/GHSA-44pw-h2cw-w3vq Depends on vulnerable versions of boom Depends on vulnerable versions of hoek Depends on vulnerable versions of sntp fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/hawk hoek * Severity: high hoek subject to prototype pollution via the clone function. - https://github.com/advisories/GHSA-c429-5p7v-vgjp fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/boom/node_modules/hoek node_modules/cryptiles/node_modules/hoek node_modules/hawk/node_modules/hoek node_modules/hoek node_modules/sntp/node_modules/hoek boom * Depends on vulnerable versions of hoek node_modules/boom node_modules/cryptiles/node_modules/boom joi 0.0.2 - 14.3.1 Depends on vulnerable versions of hoek Depends on vulnerable versions of topo node_modules/joi iobroker.yeelight-2 >=1.0.0 Depends on vulnerable versions of joi node_modules/iobroker.yeelight-2 sntp 0.0.0 || >=0.1.1 Depends on vulnerable versions of hoek node_modules/sntp topo * Depends on vulnerable versions of hoek node_modules/topo ip <1.1.9 || =2.0.0 Severity: moderate NPM IP package incorrectly identifies some private IP addresses as public - https://github.com/advisories/GHSA-78xj-cgh5-2h22 NPM IP package incorrectly identifies some private IP addresses as public - https://github.com/advisories/GHSA-78xj-cgh5-2h22 fix available via `npm audit fix` node_modules/iobroker.nuki-extended/node_modules/ip node_modules/ip js-yaml <=3.13.0 Severity: high Denial of Service in js-yaml - https://github.com/advisories/GHSA-2pr6-76vf-7546 Code Injection in js-yaml - https://github.com/advisories/GHSA-8j8c-7jfh-h6hx fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/js-yaml jscs >=1.11.2 Depends on vulnerable versions of js-yaml Depends on vulnerable versions of jscs-jsdoc Depends on vulnerable versions of lodash Depends on vulnerable versions of pathval Depends on vulnerable versions of xmlbuilder node_modules/jscs jscs-loader * Depends on vulnerable versions of jscs Depends on vulnerable versions of loader-utils node_modules/jscs-loader avrgirl-arduino 4.0.1 - 5.0.0 Depends on vulnerable versions of jscs-loader node_modules/avrgirl-arduino json5 <1.0.2 Severity: high Prototype Pollution in JSON5 via Parse Method - https://github.com/advisories/GHSA-9c47-m6qq-7p4h fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/json5 node_modules/loader-utils/node_modules/json5 loader-utils <=1.4.0 Depends on vulnerable versions of json5 node_modules/loader-utils lodash <=4.17.20 Severity: critical Regular Expression Denial of Service (ReDoS) in lodash - https://github.com/advisories/GHSA-x5rq-j2xg-h7qm Prototype Pollution in lodash - https://github.com/advisories/GHSA-fvqr-27wr-82fm Prototype Pollution in lodash - https://github.com/advisories/GHSA-jf85-cpcp-j695 Prototype Pollution in lodash - https://github.com/advisories/GHSA-4xc9-xhrj-v574 Regular Expression Denial of Service (ReDoS) in lodash - https://github.com/advisories/GHSA-29mw-wpgm-hmr9 Prototype Pollution in lodash - https://github.com/advisories/GHSA-p6mc-m468-83gw Command Injection in lodash - https://github.com/advisories/GHSA-35jh-r3h4-6jhm fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/lodash node_modules/jsdoctypeparser/node_modules/lodash jsdoctypeparser 1.2.0 - 2.0.0-alpha-5 Depends on vulnerable versions of lodash node_modules/jsdoctypeparser jscs-jsdoc >=1.1.0 Depends on vulnerable versions of jsdoctypeparser node_modules/jscs-jsdoc xmlbuilder 2.5.0 - 4.2.0 Depends on vulnerable versions of lodash node_modules/jscs/node_modules/xmlbuilder minimatch <3.0.5 Severity: high minimatch ReDoS vulnerability - https://github.com/advisories/GHSA-f8q6-p94x-37v3 fix available via `npm audit fix` node_modules/minimatch minimist <=0.2.3 Severity: critical Prototype Pollution in minimist - https://github.com/advisories/GHSA-vh95-rmgr-6w4m Prototype Pollution in minimist - https://github.com/advisories/GHSA-xvch-5gv4-984h fix available via `npm audit fix --force` Will install iobroker@2.0.3, which is a breaking change node_modules/optimist/node_modules/minimist node_modules/syno/node_modules/minimist optimist >=0.6.0 Depends on vulnerable versions of minimist node_modules/optimist node-windows 0.1.5 - 1.0.0-beta.6 Depends on vulnerable versions of optimist node_modules/node-windows iobroker >=4.0.2 Depends on vulnerable versions of node-windows node_modules/iobroker ms <2.0.0 Severity: moderate Vercel ms Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-w9mr-4mfr-499f fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/engine.io-client/node_modules/ms node_modules/mdns-discovery/node_modules/ms node_modules/socket.io-client/node_modules/ms node_modules/socket.io-client/node_modules/socket.io-parser/node_modules/ms nconf <0.11.4 Severity: high Prototype Pollution in nconf - https://github.com/advisories/GHSA-6xwr-q98w-rvg7 No fix available node_modules/nconf nedb * Severity: critical Prototype Pollution in nedb - https://github.com/advisories/GHSA-339j-hqgx-qrrx Depends on vulnerable versions of binary-search-tree Depends on vulnerable versions of underscore fix available via `npm audit fix --force` Will install iobroker.zigbee2mqtt@0.2.0, which is a breaking change node_modules/nedb aedes-persistence-nedb * Depends on vulnerable versions of nedb node_modules/aedes-persistence-nedb iobroker.zigbee2mqtt >=1.0.0 Depends on vulnerable versions of aedes-persistence-nedb node_modules/iobroker.zigbee2mqtt node-forge <=1.2.1 Severity: high Prototype Pollution in node-forge debug API. - https://github.com/advisories/GHSA-5rrq-pxf6-6jx5 Prototype Pollution in node-forge util.setPath API - https://github.com/advisories/GHSA-wxgw-qj99-44c2 URL parsing in node-forge could lead to undesired behavior. - https://github.com/advisories/GHSA-gf8q-jrpm-jvxq Improper Verification of Cryptographic Signature in `node-forge` - https://github.com/advisories/GHSA-2r2c-g63r-vccr Open Redirect in node-forge - https://github.com/advisories/GHSA-8fr3-hfg3-gpgp Prototype Pollution in node-forge - https://github.com/advisories/GHSA-92xj-mqp7-vmcj Improper Verification of Cryptographic Signature in node-forge - https://github.com/advisories/GHSA-cfm4-qjh2-4765 Improper Verification of Cryptographic Signature in node-forge - https://github.com/advisories/GHSA-x4jg-mjrx-434g fix available via `npm audit fix --force` Will install iobroker.tuya@2.0.4, which is a breaking change node_modules/adbkit/node_modules/node-forge node_modules/http-mitm-proxy/node_modules/node-forge node_modules/rsa-compat/node_modules/node-forge adbkit >=2.1.0 Depends on vulnerable versions of node-forge node_modules/adbkit http-mitm-proxy <=0.9.0 Depends on vulnerable versions of node-forge node_modules/http-mitm-proxy iobroker.tuya >=3.0.0 Depends on vulnerable versions of http-mitm-proxy node_modules/iobroker.tuya rsa-compat <=1.9.4 Depends on vulnerable versions of node-forge node_modules/rsa-compat nodemailer <=6.9.8 Severity: moderate nodemailer ReDoS when trying to send a specially crafted email - https://github.com/advisories/GHSA-9h6g-pr28-7cqp fix available via `npm audit fix` node_modules/nodemailer octokit <3.1.2 Severity: high Unauthenticated Denial of Service in the octokit/webhooks library - https://github.com/advisories/GHSA-pwfr-8pq7-x9qv fix available via `npm audit fix --force` Will install iobroker.esphome@0.2.4, which is a breaking change node_modules/octokit autopy >=1.0.0 Depends on vulnerable versions of octokit node_modules/autopy iobroker.esphome >=0.3.0 Depends on vulnerable versions of autopy node_modules/iobroker.esphome parsejson * Severity: high Regular Expression Denial of Service in parsejson - https://github.com/advisories/GHSA-q75g-2496-mxpp fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/parsejson pathval <1.1.1 Severity: high Prototype pollution in pathval - https://github.com/advisories/GHSA-g6ww-v8xp-vmwg fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/pathval put * Sensitive Data Exposure in put - https://github.com/advisories/GHSA-v6gv-fg46-h89j No fix available node_modules/put binrpc * Depends on vulnerable versions of put node_modules/binrpc iobroker.hm-rpc * Depends on vulnerable versions of binrpc node_modules/iobroker.hm-rpc qs 6.5.0 - 6.5.2 Severity: high qs vulnerable to Prototype Pollution - https://github.com/advisories/GHSA-hrpp-h998-j3pp fix available via `npm audit fix` node_modules/request/node_modules/qs semver <=5.7.1 || 6.0.0 - 6.3.0 || 7.0.0 - 7.5.1 Severity: moderate semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw fix available via `npm audit fix --force` Will install iobroker.jarvis@3.1.3, which is a breaking change node_modules/harmonyhubws/node_modules/semver node_modules/make-dir/node_modules/semver node_modules/node-abi/node_modules/semver node_modules/semver ssh2 <1.4.0 Severity: high OS Command Injection in ssh2 - https://github.com/advisories/GHSA-652h-xwhf-q4h6 No fix available node_modules/iobroker.asuswrt/node_modules/ssh2 iobroker.asuswrt * Depends on vulnerable versions of ssh2 node_modules/iobroker.asuswrt tar <6.2.1 Severity: moderate Denial of service while parsing a tar file due to lack of folders count validation - https://github.com/advisories/GHSA-f5x3-32g6-xq36 fix available via `npm audit fix` node_modules/tar tough-cookie <4.1.3 Severity: moderate tough-cookie Prototype Pollution vulnerability - https://github.com/advisories/GHSA-72xf-g2v4-qvf3 fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/machinepack-http/node_modules/tough-cookie node_modules/node-blink-security/node_modules/tough-cookie node_modules/request-promise-native/node_modules/tough-cookie node_modules/request-promise/node_modules/tough-cookie node_modules/request/node_modules/tough-cookie underscore 1.3.2 - 1.12.0 Severity: critical Arbitrary Code Execution in underscore - https://github.com/advisories/GHSA-cf4h-3jhx-xvhq fix available via `npm audit fix --force` Will install iobroker.zigbee2mqtt@0.2.0, which is a breaking change node_modules/binary-search-tree/node_modules/underscore node_modules/nedb/node_modules/underscore node_modules/nomnom/node_modules/underscore binary-search-tree * Depends on vulnerable versions of underscore node_modules/binary-search-tree nomnom >=1.6.0 Depends on vulnerable versions of underscore node_modules/nomnom validator <13.7.0 Severity: moderate Inefficient Regular Expression Complexity in validator.js - https://github.com/advisories/GHSA-qgmg-gppg-76g5 fix available via `npm audit fix` node_modules/z-schema/node_modules/validator z-schema 3.6.1 - 4.2.3 || 5.0.0 Depends on vulnerable versions of validator node_modules/z-schema xml2js <0.5.0 Severity: moderate xml2js is vulnerable to prototype pollution - https://github.com/advisories/GHSA-776f-qx25-q3cc fix available via `npm audit fix --force` Will install iobroker.radar2@1.2.5, which is a breaking change node_modules/xml2js 142 vulnerabilities (11 low, 70 moderate, 41 high, 20 critical) To address issues that do not require attention, run: npm audit fix To address all issues possible (including breaking changes), run: npm audit fix --force Some issues need review, and may require choosing a different dependency. -
@mcm57 @apollon77
Heute im log entdeckt:Nach npm audit kam folgender Vorschlag:
To address issues that do not require attention, run:
npm audit fixTo address all issues possible (including breaking changes), run:
npm audit fix --forceSome issues need review, and may require choosing
a different dependency.
Was soll ich tun?2024-04-21 04:15:05.778 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.779 - error: javascript.0 (1981571) WARN deprecated har-validator@5.1.5: this library is no longer supported 2024-04-21 04:15:05.813 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.813 - error: javascript.0 (1981571) WARN deprecated node-inspect@2.0.0: This module is part of Node.js core and does not need to be installed separately. It is now unmaintained. 2024-04-21 04:15:05.842 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.843 - error: javascript.0 (1981571) WARN deprecated uuid@3.4.0: Please upgrade to version 7 or higher. Older versions may use Math.random() in certain circumstances, which is known to be problematic. See https://v8.dev/blog/math-random for details. 2024-04-21 04:15:05.861 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.861 - error: javascript.0 (1981571) WARN deprecated request@2.88.2: request has been deprecated, see https://github.com/request/request/issues/3142 2024-04-21 04:15:07.405 - info: javascript.0 (1981571) added 98 packages, and audited 103 packages in 4s 2024-04-21 04:15:07.406 - info: javascript.0 (1981571) 4 packages are looking for funding run `npm fund` for details 2024-04-21 04:15:07.409 - info: javascript.0 (1981571) 2 moderate severity vulnerabilities Some issues need review, and may require choosing a different dependency. Run `npm audit` for details.erich@smarthome:~$ cd /opt/iobroker erich@smarthome:/opt/iobroker$ npm audit [sudo] password for erich: # npm audit report @octokit/webhooks 10.0.0 - 10.9.1 Severity: high Unauthenticated Denial of Service in the octokit/webhooks library - https://github.com/advisories/GHSA-pwfr-8pq7-x9qv fix available via `npm audit fix` node_modules/@octokit/webhooks ajv <6.12.3 Severity: moderate Prototype Pollution in Ajv - https://github.com/advisories/GHSA-v88g-cgmw-v5xw fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/node-blink-security/node_modules/ajv har-validator 3.3.0 - 5.1.0 Depends on vulnerable versions of ajv node_modules/node-blink-security/node_modules/har-validator request * Depends on vulnerable versions of har-validator Depends on vulnerable versions of hawk Depends on vulnerable versions of tough-cookie node_modules/machinepack-http/node_modules/request node_modules/node-blink-security/node_modules/request node_modules/request dropbox-v2-api * Depends on vulnerable versions of request node_modules/dropbox-v2-api iobroker.backitup >=0.3.0 Depends on vulnerable versions of dropbox-v2-api node_modules/iobroker.backitup harmonyhubws * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-native node_modules/harmonyhubws iobroker.harmony >=1.1.1 Depends on vulnerable versions of harmonyhubws node_modules/iobroker.harmony iobroker.deconz >=0.2.0 Depends on vulnerable versions of request node_modules/iobroker.deconz iobroker.hue-extended * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/iobroker.hue-extended iobroker.javascript * Depends on vulnerable versions of request node_modules/iobroker.javascript iobroker.mihome-vacuum >=2.0.7 Depends on vulnerable versions of request node_modules/iobroker.mihome-vacuum iobroker.netatmo 0.5.0 - 0.5.1 || >=1.1.7 Depends on vulnerable versions of request node_modules/iobroker.netatmo iobroker.netatmo-crawler * Depends on vulnerable versions of request node_modules/iobroker.netatmo-crawler iobroker.nuki-extended * Depends on vulnerable versions of nuki-web-api Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/iobroker.nuki-extended iobroker.rflink >=1.0.3 Depends on vulnerable versions of avrgirl-arduino Depends on vulnerable versions of request node_modules/iobroker.rflink iobroker.smartgarden >=0.5.1 Depends on vulnerable versions of request node_modules/iobroker.smartgarden iobroker.whatsapp-cmb * Depends on vulnerable versions of request node_modules/iobroker.whatsapp-cmb le-acme-core * Depends on vulnerable versions of request Depends on vulnerable versions of rsa-compat node_modules/le-acme-core iobroker.js-controller >=1.5.4 Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-adapter Depends on vulnerable versions of @iobroker/js-controller-cli Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db Depends on vulnerable versions of le-acme-core node_modules/iobroker.js-controller machinepack-http 0.2.3 - 8.0.0 Depends on vulnerable versions of request node_modules/machinepack-http bagpipes * Depends on vulnerable versions of machinepack-http node_modules/bagpipes node-blink-security * Depends on vulnerable versions of request node_modules/node-blink-security iobroker.blink4home * Depends on vulnerable versions of node-blink-security node_modules/iobroker.blink4home node-gyp <=7.1.2 Depends on vulnerable versions of request node_modules/usocket/node_modules/node-gyp usocket 0.2.2 - 0.3.0 Depends on vulnerable versions of node-gyp node_modules/usocket dbus-next * Depends on vulnerable versions of usocket Depends on vulnerable versions of xml2js node_modules/dbus-next node-ble >=0.0.2 Depends on vulnerable versions of dbus-next node_modules/node-ble iobroker.radar2 >=2.0.0 Depends on vulnerable versions of node-ble node_modules/iobroker.radar2 nuki-web-api * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/nuki-web-api request-promise >=0.0.2 Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-core Depends on vulnerable versions of tough-cookie node_modules/request-promise samsungtv Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/samsungtv iobroker.samsung >=0.5.1 Depends on vulnerable versions of samsungtv node_modules/iobroker.samsung request-promise-core * Depends on vulnerable versions of request node_modules/@cypress/request-promise/node_modules/request-promise-core node_modules/request-promise-core @cypress/request-promise * Depends on vulnerable versions of request-promise-core node_modules/@cypress/request-promise node-telegram-bot-api >=0.64.0 Depends on vulnerable versions of @cypress/request-promise node_modules/node-telegram-bot-api iobroker.telegram >=2.1.0 Depends on vulnerable versions of node-telegram-bot-api node_modules/iobroker.telegram request-promise-native >=1.0.0 Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-core Depends on vulnerable versions of tough-cookie node_modules/request-promise-native smartmeter-obis * Depends on vulnerable versions of request node_modules/smartmeter-obis iobroker.smartmeter * Depends on vulnerable versions of smartmeter-obis node_modules/iobroker.smartmeter syno * Depends on vulnerable versions of nconf Depends on vulnerable versions of request node_modules/syno iobroker.synology * Depends on vulnerable versions of syno node_modules/iobroker.synology axios <=0.27.2 || 1.0.0 - 1.5.1 Severity: high Axios vulnerable to Server-Side Request Forgery - https://github.com/advisories/GHSA-4w2v-q235-vp99 axios Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-cph5-m8f7-6c5x Axios Cross-Site Request Forgery Vulnerability - https://github.com/advisories/GHSA-wf5p-g6vw-rhxx Axios Cross-Site Request Forgery Vulnerability - https://github.com/advisories/GHSA-wf5p-g6vw-rhxx Depends on vulnerable versions of follow-redirects fix available via `npm audit fix --force` Will install iobroker.hue@0.6.0, which is a breaking change node_modules/@alcalzone/pak/node_modules/axios node_modules/iobroker.awattar/node_modules/axios node_modules/iobroker.broadlink2/node_modules/axios node_modules/iobroker.withings/node_modules/axios node_modules/node-hue-api/node_modules/axios node_modules/node-ical/node_modules/axios @alcalzone/pak 0.3.0 - 0.10.0 Depends on vulnerable versions of axios node_modules/@alcalzone/pak @iobroker/js-controller-adapter * Depends on vulnerable versions of @alcalzone/pak Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db node_modules/@iobroker/js-controller-adapter @iobroker/js-controller-common * Depends on vulnerable versions of @alcalzone/pak node_modules/@iobroker/js-controller-common @iobroker/db-base >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/js-controller-common node_modules/@iobroker/db-base @iobroker/db-objects-file >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-objects-redis node_modules/@iobroker/db-objects-file @iobroker/db-objects-jsonl >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-redis node_modules/@iobroker/db-objects-jsonl @iobroker/db-objects-redis >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base node_modules/@iobroker/db-objects-redis @iobroker/db-states-file >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-states-redis node_modules/@iobroker/db-states-file @iobroker/db-states-jsonl >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-redis node_modules/@iobroker/db-states-jsonl @iobroker/db-states-redis >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base node_modules/@iobroker/db-states-redis @iobroker/js-controller-cli * Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db node_modules/@iobroker/js-controller-cli @iobroker/js-controller-common-db * Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-common node_modules/@iobroker/js-controller-common-db iobroker.awattar >=1.0.6 Depends on vulnerable versions of axios node_modules/iobroker.awattar iobroker.broadlink2 >=2.1.0 Depends on vulnerable versions of axios node_modules/iobroker.broadlink2 iobroker.withings * Depends on vulnerable versions of axios node_modules/iobroker.withings node-hue-api 2.0.0-RC1 - 5.0.0-alpha.2 Depends on vulnerable versions of axios node_modules/node-hue-api iobroker.hue >=0.6.2 Depends on vulnerable versions of node-hue-api node_modules/iobroker.hue node-ical 0.15.3 - 0.16.1 Depends on vulnerable versions of axios node_modules/node-ical iobroker.jarvis >=3.1.3 Depends on vulnerable versions of node-ical Depends on vulnerable versions of semver node_modules/iobroker.jarvis cookiejar <2.1.4 Severity: moderate cookiejar Regular Expression Denial of Service via Cookie.parse function - https://github.com/advisories/GHSA-h452-7996-h45h fix available via `npm audit fix` node_modules/cookiejar cryptiles * Severity: critical Insufficient Entropy in cryptiles - https://github.com/advisories/GHSA-rq8g-5pc5-wrhr Depends on vulnerable versions of boom fix available via `npm audit fix` node_modules/cryptiles debug <=2.6.8 || 4.0.0 - 4.3.0 Severity: high debug Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-9vvw-cc9w-f27h Regular Expression Denial of Service in debug - https://github.com/advisories/GHSA-gxpj-cx7g-858c Regular Expression Denial of Service in debug - https://github.com/advisories/GHSA-gxpj-cx7g-858c Depends on vulnerable versions of ms fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/engine.io-client/node_modules/debug node_modules/iobroker.socketio/node_modules/debug node_modules/mdns-discovery/node_modules/debug node_modules/socket.io-client/node_modules/debug node_modules/socket.io-client/node_modules/socket.io-parser/node_modules/debug engine.io 3.4.0 - 4.0.5 Depends on vulnerable versions of debug node_modules/iobroker.socketio/node_modules/engine.io socket.io 2.2.0 - 3.0.4 Depends on vulnerable versions of debug Depends on vulnerable versions of engine.io Depends on vulnerable versions of socket.io-parser node_modules/iobroker.socketio/node_modules/socket.io iobroker.socketio 3.0.0 - 3.0.13 || 3.1.3 - 3.1.5 || 4.1.0 - 5.0.2 || 6.1.0 - 6.5.7 || >=6.6.0 Depends on vulnerable versions of socket.io node_modules/iobroker.socketio iobroker.web 4.2.1 - 4.3.0 || >=5.2.3 Depends on vulnerable versions of iobroker.socketio node_modules/iobroker.web engine.io-client <=3.1.1 Depends on vulnerable versions of debug Depends on vulnerable versions of parsejson node_modules/engine.io-client socket.io-client 1.0.0-pre - 2.1.1 Depends on vulnerable versions of debug Depends on vulnerable versions of engine.io-client Depends on vulnerable versions of socket.io-parser node_modules/socket.io-client iobroker.cloud <=2.4.6 || 2.8.0 - 3.0.2 || >=4.0.11 Depends on vulnerable versions of socket.io-client node_modules/iobroker.cloud mdns-discovery >=0.1.1 Depends on vulnerable versions of debug node_modules/mdns-discovery iobroker.discovery >=0.4.4 Depends on vulnerable versions of mdns-discovery node_modules/iobroker.discovery iobroker.firetv >=0.0.3 Depends on vulnerable versions of adbkit Depends on vulnerable versions of mdns-discovery node_modules/iobroker.firetv iobroker.mydlink >=1.0.0 Depends on vulnerable versions of mdns-discovery node_modules/iobroker.mydlink socket.io-parser <=3.3.2 || 3.4.0 - 4.0.2 Depends on vulnerable versions of debug Depends on vulnerable versions of debug node_modules/iobroker.socketio/node_modules/socket.io-parser node_modules/socket.io-client/node_modules/socket.io-parser deep-extend <0.5.1 Severity: critical Prototype Pollution in deep-extend - https://github.com/advisories/GHSA-hr2v-3952-633q fix available via `npm audit fix` node_modules/deref/node_modules/deep-extend deref 0.6.0 - 0.7.2 Depends on vulnerable versions of deep-extend node_modules/deref json-schema-faker 0.2.2 - 0.4.4 Depends on vulnerable versions of deref node_modules/json-schema-faker sway * Depends on vulnerable versions of json-schema-faker Depends on vulnerable versions of z-schema node_modules/sway dicer * Severity: high Crash in HeaderParser in dicer - https://github.com/advisories/GHSA-wm7h-9275-46v2 No fix available node_modules/dicer busboy <=0.3.1 Depends on vulnerable versions of dicer node_modules/multer/node_modules/busboy multer <=2.0.0-rc.3 Depends on vulnerable versions of busboy node_modules/multer swagger-node-runner-fork * Depends on vulnerable versions of bagpipes Depends on vulnerable versions of multer Depends on vulnerable versions of sway node_modules/swagger-node-runner-fork iobroker.rest-api * Depends on vulnerable versions of swagger-node-runner-fork node_modules/iobroker.rest-api follow-redirects <=1.15.5 Severity: high Exposure of Sensitive Information to an Unauthorized Actor in follow-redirects - https://github.com/advisories/GHSA-pw2r-vq6v-hr8c Exposure of sensitive information in follow-redirects - https://github.com/advisories/GHSA-74fj-2j2h-c42q Follow Redirects improperly handles URLs in the url.parse() function - https://github.com/advisories/GHSA-jchw-25xp-jwwc follow-redirects' Proxy-Authorization header kept across hosts - https://github.com/advisories/GHSA-cxjh-pqwp-8mfp fix available via `npm audit fix --force` Will install iobroker.hue@0.6.0, which is a breaking change node_modules/iobroker.broadlink2/node_modules/follow-redirects get-func-name <2.0.1 Severity: high Chaijs/get-func-name vulnerable to ReDoS - https://github.com/advisories/GHSA-4q6p-r6v2-jvc5 fix available via `npm audit fix` node_modules/get-func-name hawk <=9.0.0 Severity: high Uncontrolled Resource Consumption in Hawk - https://github.com/advisories/GHSA-44pw-h2cw-w3vq Depends on vulnerable versions of boom Depends on vulnerable versions of hoek Depends on vulnerable versions of sntp fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/hawk hoek * Severity: high hoek subject to prototype pollution via the clone function. - https://github.com/advisories/GHSA-c429-5p7v-vgjp fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/boom/node_modules/hoek node_modules/cryptiles/node_modules/hoek node_modules/hawk/node_modules/hoek node_modules/hoek node_modules/sntp/node_modules/hoek boom * Depends on vulnerable versions of hoek node_modules/boom node_modules/cryptiles/node_modules/boom joi 0.0.2 - 14.3.1 Depends on vulnerable versions of hoek Depends on vulnerable versions of topo node_modules/joi iobroker.yeelight-2 >=1.0.0 Depends on vulnerable versions of joi node_modules/iobroker.yeelight-2 sntp 0.0.0 || >=0.1.1 Depends on vulnerable versions of hoek node_modules/sntp topo * Depends on vulnerable versions of hoek node_modules/topo ip <1.1.9 || =2.0.0 Severity: moderate NPM IP package incorrectly identifies some private IP addresses as public - https://github.com/advisories/GHSA-78xj-cgh5-2h22 NPM IP package incorrectly identifies some private IP addresses as public - https://github.com/advisories/GHSA-78xj-cgh5-2h22 fix available via `npm audit fix` node_modules/iobroker.nuki-extended/node_modules/ip node_modules/ip js-yaml <=3.13.0 Severity: high Denial of Service in js-yaml - https://github.com/advisories/GHSA-2pr6-76vf-7546 Code Injection in js-yaml - https://github.com/advisories/GHSA-8j8c-7jfh-h6hx fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/js-yaml jscs >=1.11.2 Depends on vulnerable versions of js-yaml Depends on vulnerable versions of jscs-jsdoc Depends on vulnerable versions of lodash Depends on vulnerable versions of pathval Depends on vulnerable versions of xmlbuilder node_modules/jscs jscs-loader * Depends on vulnerable versions of jscs Depends on vulnerable versions of loader-utils node_modules/jscs-loader avrgirl-arduino 4.0.1 - 5.0.0 Depends on vulnerable versions of jscs-loader node_modules/avrgirl-arduino json5 <1.0.2 Severity: high Prototype Pollution in JSON5 via Parse Method - https://github.com/advisories/GHSA-9c47-m6qq-7p4h fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/json5 node_modules/loader-utils/node_modules/json5 loader-utils <=1.4.0 Depends on vulnerable versions of json5 node_modules/loader-utils lodash <=4.17.20 Severity: critical Regular Expression Denial of Service (ReDoS) in lodash - https://github.com/advisories/GHSA-x5rq-j2xg-h7qm Prototype Pollution in lodash - https://github.com/advisories/GHSA-fvqr-27wr-82fm Prototype Pollution in lodash - https://github.com/advisories/GHSA-jf85-cpcp-j695 Prototype Pollution in lodash - https://github.com/advisories/GHSA-4xc9-xhrj-v574 Regular Expression Denial of Service (ReDoS) in lodash - https://github.com/advisories/GHSA-29mw-wpgm-hmr9 Prototype Pollution in lodash - https://github.com/advisories/GHSA-p6mc-m468-83gw Command Injection in lodash - https://github.com/advisories/GHSA-35jh-r3h4-6jhm fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/lodash node_modules/jsdoctypeparser/node_modules/lodash jsdoctypeparser 1.2.0 - 2.0.0-alpha-5 Depends on vulnerable versions of lodash node_modules/jsdoctypeparser jscs-jsdoc >=1.1.0 Depends on vulnerable versions of jsdoctypeparser node_modules/jscs-jsdoc xmlbuilder 2.5.0 - 4.2.0 Depends on vulnerable versions of lodash node_modules/jscs/node_modules/xmlbuilder minimatch <3.0.5 Severity: high minimatch ReDoS vulnerability - https://github.com/advisories/GHSA-f8q6-p94x-37v3 fix available via `npm audit fix` node_modules/minimatch minimist <=0.2.3 Severity: critical Prototype Pollution in minimist - https://github.com/advisories/GHSA-vh95-rmgr-6w4m Prototype Pollution in minimist - https://github.com/advisories/GHSA-xvch-5gv4-984h fix available via `npm audit fix --force` Will install iobroker@2.0.3, which is a breaking change node_modules/optimist/node_modules/minimist node_modules/syno/node_modules/minimist optimist >=0.6.0 Depends on vulnerable versions of minimist node_modules/optimist node-windows 0.1.5 - 1.0.0-beta.6 Depends on vulnerable versions of optimist node_modules/node-windows iobroker >=4.0.2 Depends on vulnerable versions of node-windows node_modules/iobroker ms <2.0.0 Severity: moderate Vercel ms Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-w9mr-4mfr-499f fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/engine.io-client/node_modules/ms node_modules/mdns-discovery/node_modules/ms node_modules/socket.io-client/node_modules/ms node_modules/socket.io-client/node_modules/socket.io-parser/node_modules/ms nconf <0.11.4 Severity: high Prototype Pollution in nconf - https://github.com/advisories/GHSA-6xwr-q98w-rvg7 No fix available node_modules/nconf nedb * Severity: critical Prototype Pollution in nedb - https://github.com/advisories/GHSA-339j-hqgx-qrrx Depends on vulnerable versions of binary-search-tree Depends on vulnerable versions of underscore fix available via `npm audit fix --force` Will install iobroker.zigbee2mqtt@0.2.0, which is a breaking change node_modules/nedb aedes-persistence-nedb * Depends on vulnerable versions of nedb node_modules/aedes-persistence-nedb iobroker.zigbee2mqtt >=1.0.0 Depends on vulnerable versions of aedes-persistence-nedb node_modules/iobroker.zigbee2mqtt node-forge <=1.2.1 Severity: high Prototype Pollution in node-forge debug API. - https://github.com/advisories/GHSA-5rrq-pxf6-6jx5 Prototype Pollution in node-forge util.setPath API - https://github.com/advisories/GHSA-wxgw-qj99-44c2 URL parsing in node-forge could lead to undesired behavior. - https://github.com/advisories/GHSA-gf8q-jrpm-jvxq Improper Verification of Cryptographic Signature in `node-forge` - https://github.com/advisories/GHSA-2r2c-g63r-vccr Open Redirect in node-forge - https://github.com/advisories/GHSA-8fr3-hfg3-gpgp Prototype Pollution in node-forge - https://github.com/advisories/GHSA-92xj-mqp7-vmcj Improper Verification of Cryptographic Signature in node-forge - https://github.com/advisories/GHSA-cfm4-qjh2-4765 Improper Verification of Cryptographic Signature in node-forge - https://github.com/advisories/GHSA-x4jg-mjrx-434g fix available via `npm audit fix --force` Will install iobroker.tuya@2.0.4, which is a breaking change node_modules/adbkit/node_modules/node-forge node_modules/http-mitm-proxy/node_modules/node-forge node_modules/rsa-compat/node_modules/node-forge adbkit >=2.1.0 Depends on vulnerable versions of node-forge node_modules/adbkit http-mitm-proxy <=0.9.0 Depends on vulnerable versions of node-forge node_modules/http-mitm-proxy iobroker.tuya >=3.0.0 Depends on vulnerable versions of http-mitm-proxy node_modules/iobroker.tuya rsa-compat <=1.9.4 Depends on vulnerable versions of node-forge node_modules/rsa-compat nodemailer <=6.9.8 Severity: moderate nodemailer ReDoS when trying to send a specially crafted email - https://github.com/advisories/GHSA-9h6g-pr28-7cqp fix available via `npm audit fix` node_modules/nodemailer octokit <3.1.2 Severity: high Unauthenticated Denial of Service in the octokit/webhooks library - https://github.com/advisories/GHSA-pwfr-8pq7-x9qv fix available via `npm audit fix --force` Will install iobroker.esphome@0.2.4, which is a breaking change node_modules/octokit autopy >=1.0.0 Depends on vulnerable versions of octokit node_modules/autopy iobroker.esphome >=0.3.0 Depends on vulnerable versions of autopy node_modules/iobroker.esphome parsejson * Severity: high Regular Expression Denial of Service in parsejson - https://github.com/advisories/GHSA-q75g-2496-mxpp fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/parsejson pathval <1.1.1 Severity: high Prototype pollution in pathval - https://github.com/advisories/GHSA-g6ww-v8xp-vmwg fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/pathval put * Sensitive Data Exposure in put - https://github.com/advisories/GHSA-v6gv-fg46-h89j No fix available node_modules/put binrpc * Depends on vulnerable versions of put node_modules/binrpc iobroker.hm-rpc * Depends on vulnerable versions of binrpc node_modules/iobroker.hm-rpc qs 6.5.0 - 6.5.2 Severity: high qs vulnerable to Prototype Pollution - https://github.com/advisories/GHSA-hrpp-h998-j3pp fix available via `npm audit fix` node_modules/request/node_modules/qs semver <=5.7.1 || 6.0.0 - 6.3.0 || 7.0.0 - 7.5.1 Severity: moderate semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw fix available via `npm audit fix --force` Will install iobroker.jarvis@3.1.3, which is a breaking change node_modules/harmonyhubws/node_modules/semver node_modules/make-dir/node_modules/semver node_modules/node-abi/node_modules/semver node_modules/semver ssh2 <1.4.0 Severity: high OS Command Injection in ssh2 - https://github.com/advisories/GHSA-652h-xwhf-q4h6 No fix available node_modules/iobroker.asuswrt/node_modules/ssh2 iobroker.asuswrt * Depends on vulnerable versions of ssh2 node_modules/iobroker.asuswrt tar <6.2.1 Severity: moderate Denial of service while parsing a tar file due to lack of folders count validation - https://github.com/advisories/GHSA-f5x3-32g6-xq36 fix available via `npm audit fix` node_modules/tar tough-cookie <4.1.3 Severity: moderate tough-cookie Prototype Pollution vulnerability - https://github.com/advisories/GHSA-72xf-g2v4-qvf3 fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/machinepack-http/node_modules/tough-cookie node_modules/node-blink-security/node_modules/tough-cookie node_modules/request-promise-native/node_modules/tough-cookie node_modules/request-promise/node_modules/tough-cookie node_modules/request/node_modules/tough-cookie underscore 1.3.2 - 1.12.0 Severity: critical Arbitrary Code Execution in underscore - https://github.com/advisories/GHSA-cf4h-3jhx-xvhq fix available via `npm audit fix --force` Will install iobroker.zigbee2mqtt@0.2.0, which is a breaking change node_modules/binary-search-tree/node_modules/underscore node_modules/nedb/node_modules/underscore node_modules/nomnom/node_modules/underscore binary-search-tree * Depends on vulnerable versions of underscore node_modules/binary-search-tree nomnom >=1.6.0 Depends on vulnerable versions of underscore node_modules/nomnom validator <13.7.0 Severity: moderate Inefficient Regular Expression Complexity in validator.js - https://github.com/advisories/GHSA-qgmg-gppg-76g5 fix available via `npm audit fix` node_modules/z-schema/node_modules/validator z-schema 3.6.1 - 4.2.3 || 5.0.0 Depends on vulnerable versions of validator node_modules/z-schema xml2js <0.5.0 Severity: moderate xml2js is vulnerable to prototype pollution - https://github.com/advisories/GHSA-776f-qx25-q3cc fix available via `npm audit fix --force` Will install iobroker.radar2@1.2.5, which is a breaking change node_modules/xml2js 142 vulnerabilities (11 low, 70 moderate, 41 high, 20 critical) To address issues that do not require attention, run: npm audit fix To address all issues possible (including breaking changes), run: npm audit fix --force Some issues need review, and may require choosing a different dependency.@muckel sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
Was soll ich tun?
Die Finger von npm audit fix lassen. Inbesondere von --force.
-
@muckel sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
Was soll ich tun?
Die Finger von npm audit fix lassen. Inbesondere von --force.
Danke, hätte ich eh nicht gemacht. ;-)
Ich warte auf einen Fix, oder Workaround von den Profis.
lg. erich -
@mcm57 @apollon77
Heute im log entdeckt:Nach npm audit kam folgender Vorschlag:
To address issues that do not require attention, run:
npm audit fixTo address all issues possible (including breaking changes), run:
npm audit fix --forceSome issues need review, and may require choosing
a different dependency.
Was soll ich tun?2024-04-21 04:15:05.778 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.779 - error: javascript.0 (1981571) WARN deprecated har-validator@5.1.5: this library is no longer supported 2024-04-21 04:15:05.813 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.813 - error: javascript.0 (1981571) WARN deprecated node-inspect@2.0.0: This module is part of Node.js core and does not need to be installed separately. It is now unmaintained. 2024-04-21 04:15:05.842 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.843 - error: javascript.0 (1981571) WARN deprecated uuid@3.4.0: Please upgrade to version 7 or higher. Older versions may use Math.random() in certain circumstances, which is known to be problematic. See https://v8.dev/blog/math-random for details. 2024-04-21 04:15:05.861 - error: javascript.0 (1981571) npm 2024-04-21 04:15:05.861 - error: javascript.0 (1981571) WARN deprecated request@2.88.2: request has been deprecated, see https://github.com/request/request/issues/3142 2024-04-21 04:15:07.405 - info: javascript.0 (1981571) added 98 packages, and audited 103 packages in 4s 2024-04-21 04:15:07.406 - info: javascript.0 (1981571) 4 packages are looking for funding run `npm fund` for details 2024-04-21 04:15:07.409 - info: javascript.0 (1981571) 2 moderate severity vulnerabilities Some issues need review, and may require choosing a different dependency. Run `npm audit` for details.erich@smarthome:~$ cd /opt/iobroker erich@smarthome:/opt/iobroker$ npm audit [sudo] password for erich: # npm audit report @octokit/webhooks 10.0.0 - 10.9.1 Severity: high Unauthenticated Denial of Service in the octokit/webhooks library - https://github.com/advisories/GHSA-pwfr-8pq7-x9qv fix available via `npm audit fix` node_modules/@octokit/webhooks ajv <6.12.3 Severity: moderate Prototype Pollution in Ajv - https://github.com/advisories/GHSA-v88g-cgmw-v5xw fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/node-blink-security/node_modules/ajv har-validator 3.3.0 - 5.1.0 Depends on vulnerable versions of ajv node_modules/node-blink-security/node_modules/har-validator request * Depends on vulnerable versions of har-validator Depends on vulnerable versions of hawk Depends on vulnerable versions of tough-cookie node_modules/machinepack-http/node_modules/request node_modules/node-blink-security/node_modules/request node_modules/request dropbox-v2-api * Depends on vulnerable versions of request node_modules/dropbox-v2-api iobroker.backitup >=0.3.0 Depends on vulnerable versions of dropbox-v2-api node_modules/iobroker.backitup harmonyhubws * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-native node_modules/harmonyhubws iobroker.harmony >=1.1.1 Depends on vulnerable versions of harmonyhubws node_modules/iobroker.harmony iobroker.deconz >=0.2.0 Depends on vulnerable versions of request node_modules/iobroker.deconz iobroker.hue-extended * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/iobroker.hue-extended iobroker.javascript * Depends on vulnerable versions of request node_modules/iobroker.javascript iobroker.mihome-vacuum >=2.0.7 Depends on vulnerable versions of request node_modules/iobroker.mihome-vacuum iobroker.netatmo 0.5.0 - 0.5.1 || >=1.1.7 Depends on vulnerable versions of request node_modules/iobroker.netatmo iobroker.netatmo-crawler * Depends on vulnerable versions of request node_modules/iobroker.netatmo-crawler iobroker.nuki-extended * Depends on vulnerable versions of nuki-web-api Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/iobroker.nuki-extended iobroker.rflink >=1.0.3 Depends on vulnerable versions of avrgirl-arduino Depends on vulnerable versions of request node_modules/iobroker.rflink iobroker.smartgarden >=0.5.1 Depends on vulnerable versions of request node_modules/iobroker.smartgarden iobroker.whatsapp-cmb * Depends on vulnerable versions of request node_modules/iobroker.whatsapp-cmb le-acme-core * Depends on vulnerable versions of request Depends on vulnerable versions of rsa-compat node_modules/le-acme-core iobroker.js-controller >=1.5.4 Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-adapter Depends on vulnerable versions of @iobroker/js-controller-cli Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db Depends on vulnerable versions of le-acme-core node_modules/iobroker.js-controller machinepack-http 0.2.3 - 8.0.0 Depends on vulnerable versions of request node_modules/machinepack-http bagpipes * Depends on vulnerable versions of machinepack-http node_modules/bagpipes node-blink-security * Depends on vulnerable versions of request node_modules/node-blink-security iobroker.blink4home * Depends on vulnerable versions of node-blink-security node_modules/iobroker.blink4home node-gyp <=7.1.2 Depends on vulnerable versions of request node_modules/usocket/node_modules/node-gyp usocket 0.2.2 - 0.3.0 Depends on vulnerable versions of node-gyp node_modules/usocket dbus-next * Depends on vulnerable versions of usocket Depends on vulnerable versions of xml2js node_modules/dbus-next node-ble >=0.0.2 Depends on vulnerable versions of dbus-next node_modules/node-ble iobroker.radar2 >=2.0.0 Depends on vulnerable versions of node-ble node_modules/iobroker.radar2 nuki-web-api * Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/nuki-web-api request-promise >=0.0.2 Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-core Depends on vulnerable versions of tough-cookie node_modules/request-promise samsungtv Depends on vulnerable versions of request Depends on vulnerable versions of request-promise node_modules/samsungtv iobroker.samsung >=0.5.1 Depends on vulnerable versions of samsungtv node_modules/iobroker.samsung request-promise-core * Depends on vulnerable versions of request node_modules/@cypress/request-promise/node_modules/request-promise-core node_modules/request-promise-core @cypress/request-promise * Depends on vulnerable versions of request-promise-core node_modules/@cypress/request-promise node-telegram-bot-api >=0.64.0 Depends on vulnerable versions of @cypress/request-promise node_modules/node-telegram-bot-api iobroker.telegram >=2.1.0 Depends on vulnerable versions of node-telegram-bot-api node_modules/iobroker.telegram request-promise-native >=1.0.0 Depends on vulnerable versions of request Depends on vulnerable versions of request-promise-core Depends on vulnerable versions of tough-cookie node_modules/request-promise-native smartmeter-obis * Depends on vulnerable versions of request node_modules/smartmeter-obis iobroker.smartmeter * Depends on vulnerable versions of smartmeter-obis node_modules/iobroker.smartmeter syno * Depends on vulnerable versions of nconf Depends on vulnerable versions of request node_modules/syno iobroker.synology * Depends on vulnerable versions of syno node_modules/iobroker.synology axios <=0.27.2 || 1.0.0 - 1.5.1 Severity: high Axios vulnerable to Server-Side Request Forgery - https://github.com/advisories/GHSA-4w2v-q235-vp99 axios Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-cph5-m8f7-6c5x Axios Cross-Site Request Forgery Vulnerability - https://github.com/advisories/GHSA-wf5p-g6vw-rhxx Axios Cross-Site Request Forgery Vulnerability - https://github.com/advisories/GHSA-wf5p-g6vw-rhxx Depends on vulnerable versions of follow-redirects fix available via `npm audit fix --force` Will install iobroker.hue@0.6.0, which is a breaking change node_modules/@alcalzone/pak/node_modules/axios node_modules/iobroker.awattar/node_modules/axios node_modules/iobroker.broadlink2/node_modules/axios node_modules/iobroker.withings/node_modules/axios node_modules/node-hue-api/node_modules/axios node_modules/node-ical/node_modules/axios @alcalzone/pak 0.3.0 - 0.10.0 Depends on vulnerable versions of axios node_modules/@alcalzone/pak @iobroker/js-controller-adapter * Depends on vulnerable versions of @alcalzone/pak Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db node_modules/@iobroker/js-controller-adapter @iobroker/js-controller-common * Depends on vulnerable versions of @alcalzone/pak node_modules/@iobroker/js-controller-common @iobroker/db-base >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/js-controller-common node_modules/@iobroker/db-base @iobroker/db-objects-file >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-objects-redis node_modules/@iobroker/db-objects-file @iobroker/db-objects-jsonl >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-redis node_modules/@iobroker/db-objects-jsonl @iobroker/db-objects-redis >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base node_modules/@iobroker/db-objects-redis @iobroker/db-states-file >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-states-redis node_modules/@iobroker/db-states-file @iobroker/db-states-jsonl >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-redis node_modules/@iobroker/db-states-jsonl @iobroker/db-states-redis >=4.0.0-alpha.1-20210830-d9828cd3 Depends on vulnerable versions of @iobroker/db-base node_modules/@iobroker/db-states-redis @iobroker/js-controller-cli * Depends on vulnerable versions of @iobroker/js-controller-common Depends on vulnerable versions of @iobroker/js-controller-common-db node_modules/@iobroker/js-controller-cli @iobroker/js-controller-common-db * Depends on vulnerable versions of @iobroker/db-objects-file Depends on vulnerable versions of @iobroker/db-objects-jsonl Depends on vulnerable versions of @iobroker/db-objects-redis Depends on vulnerable versions of @iobroker/db-states-file Depends on vulnerable versions of @iobroker/db-states-jsonl Depends on vulnerable versions of @iobroker/db-states-redis Depends on vulnerable versions of @iobroker/js-controller-common node_modules/@iobroker/js-controller-common-db iobroker.awattar >=1.0.6 Depends on vulnerable versions of axios node_modules/iobroker.awattar iobroker.broadlink2 >=2.1.0 Depends on vulnerable versions of axios node_modules/iobroker.broadlink2 iobroker.withings * Depends on vulnerable versions of axios node_modules/iobroker.withings node-hue-api 2.0.0-RC1 - 5.0.0-alpha.2 Depends on vulnerable versions of axios node_modules/node-hue-api iobroker.hue >=0.6.2 Depends on vulnerable versions of node-hue-api node_modules/iobroker.hue node-ical 0.15.3 - 0.16.1 Depends on vulnerable versions of axios node_modules/node-ical iobroker.jarvis >=3.1.3 Depends on vulnerable versions of node-ical Depends on vulnerable versions of semver node_modules/iobroker.jarvis cookiejar <2.1.4 Severity: moderate cookiejar Regular Expression Denial of Service via Cookie.parse function - https://github.com/advisories/GHSA-h452-7996-h45h fix available via `npm audit fix` node_modules/cookiejar cryptiles * Severity: critical Insufficient Entropy in cryptiles - https://github.com/advisories/GHSA-rq8g-5pc5-wrhr Depends on vulnerable versions of boom fix available via `npm audit fix` node_modules/cryptiles debug <=2.6.8 || 4.0.0 - 4.3.0 Severity: high debug Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-9vvw-cc9w-f27h Regular Expression Denial of Service in debug - https://github.com/advisories/GHSA-gxpj-cx7g-858c Regular Expression Denial of Service in debug - https://github.com/advisories/GHSA-gxpj-cx7g-858c Depends on vulnerable versions of ms fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/engine.io-client/node_modules/debug node_modules/iobroker.socketio/node_modules/debug node_modules/mdns-discovery/node_modules/debug node_modules/socket.io-client/node_modules/debug node_modules/socket.io-client/node_modules/socket.io-parser/node_modules/debug engine.io 3.4.0 - 4.0.5 Depends on vulnerable versions of debug node_modules/iobroker.socketio/node_modules/engine.io socket.io 2.2.0 - 3.0.4 Depends on vulnerable versions of debug Depends on vulnerable versions of engine.io Depends on vulnerable versions of socket.io-parser node_modules/iobroker.socketio/node_modules/socket.io iobroker.socketio 3.0.0 - 3.0.13 || 3.1.3 - 3.1.5 || 4.1.0 - 5.0.2 || 6.1.0 - 6.5.7 || >=6.6.0 Depends on vulnerable versions of socket.io node_modules/iobroker.socketio iobroker.web 4.2.1 - 4.3.0 || >=5.2.3 Depends on vulnerable versions of iobroker.socketio node_modules/iobroker.web engine.io-client <=3.1.1 Depends on vulnerable versions of debug Depends on vulnerable versions of parsejson node_modules/engine.io-client socket.io-client 1.0.0-pre - 2.1.1 Depends on vulnerable versions of debug Depends on vulnerable versions of engine.io-client Depends on vulnerable versions of socket.io-parser node_modules/socket.io-client iobroker.cloud <=2.4.6 || 2.8.0 - 3.0.2 || >=4.0.11 Depends on vulnerable versions of socket.io-client node_modules/iobroker.cloud mdns-discovery >=0.1.1 Depends on vulnerable versions of debug node_modules/mdns-discovery iobroker.discovery >=0.4.4 Depends on vulnerable versions of mdns-discovery node_modules/iobroker.discovery iobroker.firetv >=0.0.3 Depends on vulnerable versions of adbkit Depends on vulnerable versions of mdns-discovery node_modules/iobroker.firetv iobroker.mydlink >=1.0.0 Depends on vulnerable versions of mdns-discovery node_modules/iobroker.mydlink socket.io-parser <=3.3.2 || 3.4.0 - 4.0.2 Depends on vulnerable versions of debug Depends on vulnerable versions of debug node_modules/iobroker.socketio/node_modules/socket.io-parser node_modules/socket.io-client/node_modules/socket.io-parser deep-extend <0.5.1 Severity: critical Prototype Pollution in deep-extend - https://github.com/advisories/GHSA-hr2v-3952-633q fix available via `npm audit fix` node_modules/deref/node_modules/deep-extend deref 0.6.0 - 0.7.2 Depends on vulnerable versions of deep-extend node_modules/deref json-schema-faker 0.2.2 - 0.4.4 Depends on vulnerable versions of deref node_modules/json-schema-faker sway * Depends on vulnerable versions of json-schema-faker Depends on vulnerable versions of z-schema node_modules/sway dicer * Severity: high Crash in HeaderParser in dicer - https://github.com/advisories/GHSA-wm7h-9275-46v2 No fix available node_modules/dicer busboy <=0.3.1 Depends on vulnerable versions of dicer node_modules/multer/node_modules/busboy multer <=2.0.0-rc.3 Depends on vulnerable versions of busboy node_modules/multer swagger-node-runner-fork * Depends on vulnerable versions of bagpipes Depends on vulnerable versions of multer Depends on vulnerable versions of sway node_modules/swagger-node-runner-fork iobroker.rest-api * Depends on vulnerable versions of swagger-node-runner-fork node_modules/iobroker.rest-api follow-redirects <=1.15.5 Severity: high Exposure of Sensitive Information to an Unauthorized Actor in follow-redirects - https://github.com/advisories/GHSA-pw2r-vq6v-hr8c Exposure of sensitive information in follow-redirects - https://github.com/advisories/GHSA-74fj-2j2h-c42q Follow Redirects improperly handles URLs in the url.parse() function - https://github.com/advisories/GHSA-jchw-25xp-jwwc follow-redirects' Proxy-Authorization header kept across hosts - https://github.com/advisories/GHSA-cxjh-pqwp-8mfp fix available via `npm audit fix --force` Will install iobroker.hue@0.6.0, which is a breaking change node_modules/iobroker.broadlink2/node_modules/follow-redirects get-func-name <2.0.1 Severity: high Chaijs/get-func-name vulnerable to ReDoS - https://github.com/advisories/GHSA-4q6p-r6v2-jvc5 fix available via `npm audit fix` node_modules/get-func-name hawk <=9.0.0 Severity: high Uncontrolled Resource Consumption in Hawk - https://github.com/advisories/GHSA-44pw-h2cw-w3vq Depends on vulnerable versions of boom Depends on vulnerable versions of hoek Depends on vulnerable versions of sntp fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/hawk hoek * Severity: high hoek subject to prototype pollution via the clone function. - https://github.com/advisories/GHSA-c429-5p7v-vgjp fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/boom/node_modules/hoek node_modules/cryptiles/node_modules/hoek node_modules/hawk/node_modules/hoek node_modules/hoek node_modules/sntp/node_modules/hoek boom * Depends on vulnerable versions of hoek node_modules/boom node_modules/cryptiles/node_modules/boom joi 0.0.2 - 14.3.1 Depends on vulnerable versions of hoek Depends on vulnerable versions of topo node_modules/joi iobroker.yeelight-2 >=1.0.0 Depends on vulnerable versions of joi node_modules/iobroker.yeelight-2 sntp 0.0.0 || >=0.1.1 Depends on vulnerable versions of hoek node_modules/sntp topo * Depends on vulnerable versions of hoek node_modules/topo ip <1.1.9 || =2.0.0 Severity: moderate NPM IP package incorrectly identifies some private IP addresses as public - https://github.com/advisories/GHSA-78xj-cgh5-2h22 NPM IP package incorrectly identifies some private IP addresses as public - https://github.com/advisories/GHSA-78xj-cgh5-2h22 fix available via `npm audit fix` node_modules/iobroker.nuki-extended/node_modules/ip node_modules/ip js-yaml <=3.13.0 Severity: high Denial of Service in js-yaml - https://github.com/advisories/GHSA-2pr6-76vf-7546 Code Injection in js-yaml - https://github.com/advisories/GHSA-8j8c-7jfh-h6hx fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/js-yaml jscs >=1.11.2 Depends on vulnerable versions of js-yaml Depends on vulnerable versions of jscs-jsdoc Depends on vulnerable versions of lodash Depends on vulnerable versions of pathval Depends on vulnerable versions of xmlbuilder node_modules/jscs jscs-loader * Depends on vulnerable versions of jscs Depends on vulnerable versions of loader-utils node_modules/jscs-loader avrgirl-arduino 4.0.1 - 5.0.0 Depends on vulnerable versions of jscs-loader node_modules/avrgirl-arduino json5 <1.0.2 Severity: high Prototype Pollution in JSON5 via Parse Method - https://github.com/advisories/GHSA-9c47-m6qq-7p4h fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/json5 node_modules/loader-utils/node_modules/json5 loader-utils <=1.4.0 Depends on vulnerable versions of json5 node_modules/loader-utils lodash <=4.17.20 Severity: critical Regular Expression Denial of Service (ReDoS) in lodash - https://github.com/advisories/GHSA-x5rq-j2xg-h7qm Prototype Pollution in lodash - https://github.com/advisories/GHSA-fvqr-27wr-82fm Prototype Pollution in lodash - https://github.com/advisories/GHSA-jf85-cpcp-j695 Prototype Pollution in lodash - https://github.com/advisories/GHSA-4xc9-xhrj-v574 Regular Expression Denial of Service (ReDoS) in lodash - https://github.com/advisories/GHSA-29mw-wpgm-hmr9 Prototype Pollution in lodash - https://github.com/advisories/GHSA-p6mc-m468-83gw Command Injection in lodash - https://github.com/advisories/GHSA-35jh-r3h4-6jhm fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/lodash node_modules/jsdoctypeparser/node_modules/lodash jsdoctypeparser 1.2.0 - 2.0.0-alpha-5 Depends on vulnerable versions of lodash node_modules/jsdoctypeparser jscs-jsdoc >=1.1.0 Depends on vulnerable versions of jsdoctypeparser node_modules/jscs-jsdoc xmlbuilder 2.5.0 - 4.2.0 Depends on vulnerable versions of lodash node_modules/jscs/node_modules/xmlbuilder minimatch <3.0.5 Severity: high minimatch ReDoS vulnerability - https://github.com/advisories/GHSA-f8q6-p94x-37v3 fix available via `npm audit fix` node_modules/minimatch minimist <=0.2.3 Severity: critical Prototype Pollution in minimist - https://github.com/advisories/GHSA-vh95-rmgr-6w4m Prototype Pollution in minimist - https://github.com/advisories/GHSA-xvch-5gv4-984h fix available via `npm audit fix --force` Will install iobroker@2.0.3, which is a breaking change node_modules/optimist/node_modules/minimist node_modules/syno/node_modules/minimist optimist >=0.6.0 Depends on vulnerable versions of minimist node_modules/optimist node-windows 0.1.5 - 1.0.0-beta.6 Depends on vulnerable versions of optimist node_modules/node-windows iobroker >=4.0.2 Depends on vulnerable versions of node-windows node_modules/iobroker ms <2.0.0 Severity: moderate Vercel ms Inefficient Regular Expression Complexity vulnerability - https://github.com/advisories/GHSA-w9mr-4mfr-499f fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/engine.io-client/node_modules/ms node_modules/mdns-discovery/node_modules/ms node_modules/socket.io-client/node_modules/ms node_modules/socket.io-client/node_modules/socket.io-parser/node_modules/ms nconf <0.11.4 Severity: high Prototype Pollution in nconf - https://github.com/advisories/GHSA-6xwr-q98w-rvg7 No fix available node_modules/nconf nedb * Severity: critical Prototype Pollution in nedb - https://github.com/advisories/GHSA-339j-hqgx-qrrx Depends on vulnerable versions of binary-search-tree Depends on vulnerable versions of underscore fix available via `npm audit fix --force` Will install iobroker.zigbee2mqtt@0.2.0, which is a breaking change node_modules/nedb aedes-persistence-nedb * Depends on vulnerable versions of nedb node_modules/aedes-persistence-nedb iobroker.zigbee2mqtt >=1.0.0 Depends on vulnerable versions of aedes-persistence-nedb node_modules/iobroker.zigbee2mqtt node-forge <=1.2.1 Severity: high Prototype Pollution in node-forge debug API. - https://github.com/advisories/GHSA-5rrq-pxf6-6jx5 Prototype Pollution in node-forge util.setPath API - https://github.com/advisories/GHSA-wxgw-qj99-44c2 URL parsing in node-forge could lead to undesired behavior. - https://github.com/advisories/GHSA-gf8q-jrpm-jvxq Improper Verification of Cryptographic Signature in `node-forge` - https://github.com/advisories/GHSA-2r2c-g63r-vccr Open Redirect in node-forge - https://github.com/advisories/GHSA-8fr3-hfg3-gpgp Prototype Pollution in node-forge - https://github.com/advisories/GHSA-92xj-mqp7-vmcj Improper Verification of Cryptographic Signature in node-forge - https://github.com/advisories/GHSA-cfm4-qjh2-4765 Improper Verification of Cryptographic Signature in node-forge - https://github.com/advisories/GHSA-x4jg-mjrx-434g fix available via `npm audit fix --force` Will install iobroker.tuya@2.0.4, which is a breaking change node_modules/adbkit/node_modules/node-forge node_modules/http-mitm-proxy/node_modules/node-forge node_modules/rsa-compat/node_modules/node-forge adbkit >=2.1.0 Depends on vulnerable versions of node-forge node_modules/adbkit http-mitm-proxy <=0.9.0 Depends on vulnerable versions of node-forge node_modules/http-mitm-proxy iobroker.tuya >=3.0.0 Depends on vulnerable versions of http-mitm-proxy node_modules/iobroker.tuya rsa-compat <=1.9.4 Depends on vulnerable versions of node-forge node_modules/rsa-compat nodemailer <=6.9.8 Severity: moderate nodemailer ReDoS when trying to send a specially crafted email - https://github.com/advisories/GHSA-9h6g-pr28-7cqp fix available via `npm audit fix` node_modules/nodemailer octokit <3.1.2 Severity: high Unauthenticated Denial of Service in the octokit/webhooks library - https://github.com/advisories/GHSA-pwfr-8pq7-x9qv fix available via `npm audit fix --force` Will install iobroker.esphome@0.2.4, which is a breaking change node_modules/octokit autopy >=1.0.0 Depends on vulnerable versions of octokit node_modules/autopy iobroker.esphome >=0.3.0 Depends on vulnerable versions of autopy node_modules/iobroker.esphome parsejson * Severity: high Regular Expression Denial of Service in parsejson - https://github.com/advisories/GHSA-q75g-2496-mxpp fix available via `npm audit fix --force` Will install iobroker.cloud@4.0.10, which is a breaking change node_modules/parsejson pathval <1.1.1 Severity: high Prototype pollution in pathval - https://github.com/advisories/GHSA-g6ww-v8xp-vmwg fix available via `npm audit fix --force` Will install iobroker.rflink@1.0.2, which is a breaking change node_modules/jscs/node_modules/pathval put * Sensitive Data Exposure in put - https://github.com/advisories/GHSA-v6gv-fg46-h89j No fix available node_modules/put binrpc * Depends on vulnerable versions of put node_modules/binrpc iobroker.hm-rpc * Depends on vulnerable versions of binrpc node_modules/iobroker.hm-rpc qs 6.5.0 - 6.5.2 Severity: high qs vulnerable to Prototype Pollution - https://github.com/advisories/GHSA-hrpp-h998-j3pp fix available via `npm audit fix` node_modules/request/node_modules/qs semver <=5.7.1 || 6.0.0 - 6.3.0 || 7.0.0 - 7.5.1 Severity: moderate semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw semver vulnerable to Regular Expression Denial of Service - https://github.com/advisories/GHSA-c2qf-rxjj-qqgw fix available via `npm audit fix --force` Will install iobroker.jarvis@3.1.3, which is a breaking change node_modules/harmonyhubws/node_modules/semver node_modules/make-dir/node_modules/semver node_modules/node-abi/node_modules/semver node_modules/semver ssh2 <1.4.0 Severity: high OS Command Injection in ssh2 - https://github.com/advisories/GHSA-652h-xwhf-q4h6 No fix available node_modules/iobroker.asuswrt/node_modules/ssh2 iobroker.asuswrt * Depends on vulnerable versions of ssh2 node_modules/iobroker.asuswrt tar <6.2.1 Severity: moderate Denial of service while parsing a tar file due to lack of folders count validation - https://github.com/advisories/GHSA-f5x3-32g6-xq36 fix available via `npm audit fix` node_modules/tar tough-cookie <4.1.3 Severity: moderate tough-cookie Prototype Pollution vulnerability - https://github.com/advisories/GHSA-72xf-g2v4-qvf3 fix available via `npm audit fix --force` Will install iobroker.samsung@0.2.9, which is a breaking change node_modules/machinepack-http/node_modules/tough-cookie node_modules/node-blink-security/node_modules/tough-cookie node_modules/request-promise-native/node_modules/tough-cookie node_modules/request-promise/node_modules/tough-cookie node_modules/request/node_modules/tough-cookie underscore 1.3.2 - 1.12.0 Severity: critical Arbitrary Code Execution in underscore - https://github.com/advisories/GHSA-cf4h-3jhx-xvhq fix available via `npm audit fix --force` Will install iobroker.zigbee2mqtt@0.2.0, which is a breaking change node_modules/binary-search-tree/node_modules/underscore node_modules/nedb/node_modules/underscore node_modules/nomnom/node_modules/underscore binary-search-tree * Depends on vulnerable versions of underscore node_modules/binary-search-tree nomnom >=1.6.0 Depends on vulnerable versions of underscore node_modules/nomnom validator <13.7.0 Severity: moderate Inefficient Regular Expression Complexity in validator.js - https://github.com/advisories/GHSA-qgmg-gppg-76g5 fix available via `npm audit fix` node_modules/z-schema/node_modules/validator z-schema 3.6.1 - 4.2.3 || 5.0.0 Depends on vulnerable versions of validator node_modules/z-schema xml2js <0.5.0 Severity: moderate xml2js is vulnerable to prototype pollution - https://github.com/advisories/GHSA-776f-qx25-q3cc fix available via `npm audit fix --force` Will install iobroker.radar2@1.2.5, which is a breaking change node_modules/xml2js 142 vulnerabilities (11 low, 70 moderate, 41 high, 20 critical) To address issues that do not require attention, run: npm audit fix To address all issues possible (including breaking changes), run: npm audit fix --force Some issues need review, and may require choosing a different dependency. -
@muckel said in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
Ich habe in meinem Thread gelesen, dass es durch meinen Fehler doch zu Problemen kommen kann.
Siehe:
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/20
Gibt es da einen Workaround?@apollon77
Geht drum dass muckel einnpm i @iobroker/adapter-coreauf der obersten Ebene gestartet hat. Damit läuft admin zwar, aber ein explizites Install ist ja nicht "gut". Kannst du sagen ob bzw. wie das zu fixen wäre?
https://forum.iobroker.net/topic/74232/gelöst-nach-update-des-admin-adapters-kein-webzugriff-mehr/11 -
@mcm57 Lass es erstmal so ... wenn es irgendwann mal Probleme macht kann man es dann fixen ... aber vllt ists auch ok
@apollon77
Danke für die Info.
Dann lass ich es erst mal so. -
@apollon77
Danke für die Info.
Dann lass ich es erst mal so.Hallo zusammen, wollte letzte Woche bereits etwas dazu schreiben, aber da es nach dem Fix (erneut) klappte, hab ich die Idee verworfen.
Jetzt habe ich das Problem allerdings wieder. Aber von vorne:
Ich nutze ioBroker auf meiner Synology in der v9-latest.
Anscheinend habe ich im besagten Zeitraum den spotify-premium & telegram-Adapter geupdated, die versagten dann mit 'ERR_INVALID_ARG_VALUE' den Dienst. Dieses Topic war schnell ausfindig gemacht und über die obige Anleitung habe ich die Fixes eingespielt, kontrolliert und alles schien ok zu sein.
Letzte Woche ganbs ein Update der Syno, nach Reboot (der Syno und damit des Containers) standen beide Adapter wieder auf 3.12. Also das Ganze nochmal.
Ich habe jeweils den ioBroker mit "iob maintenance on" beendet, hab unter /opt/iobroker "npm list @iobroker/adapter-core" aufgerufen, bin in die Adapter-Verzeichnisse gewechselt und habe dort "npm i @iobroker/adapter-core@3.1.4". Aufgerufen.
Test mit "npm list @iobroker/adapter-core" sah gut aus (jeweils die 3.14 drauf). Danach den IOB mit "iob maintenance on" wieder gestartet. Ein weiteres "npm list @iobroker/adapter-core" zeigt mir aber jetzt├─┬ iobroker.spotify-premium@1.4.0 │ └── @iobroker/adapter-core@3.1.2 invalid: "^3.1.4" from node_modules/iobroker.spotify-premiumbzw.
iobroker.telegram@3.2.1 │ └── @iobroker/adapter-core@3.1.2 invalid: "^3.1.4" from node_modules/iobroker.telegram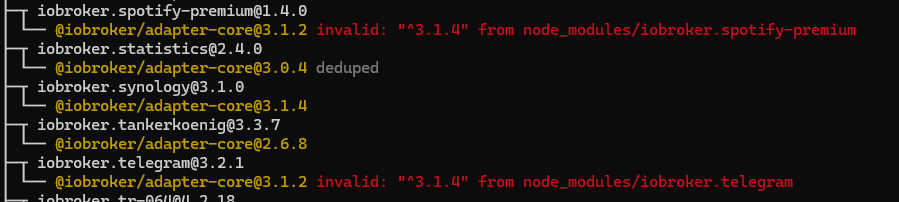
Die Ausgabe nach "npm i @iobroker/adapter-core@3.14" (bei telegram):
npm i @iobroker/adapter-core@3.1.4 sudo: unable to resolve host iobroker-v9-prod: Name or service not known npm WARN deprecated urix@0.1.0: Please see https://github.com/lydell/urix#deprecated npm WARN deprecated har-validator@5.1.5: this library is no longer supported npm WARN deprecated source-map-url@0.4.1: See https://github.com/lydell/source-map-url#deprecated npm WARN deprecated resolve-url@0.2.1: https://github.com/lydell/resolve-url#deprecated npm WARN deprecated source-map-resolve@0.5.3: See https://github.com/lydell/source-map-resolve#deprecated npm WARN deprecated uuid@3.4.0: Please upgrade to version 7 or higher. Older versions may use Math.random() in certain circumstances, which is known to be problematic. See https://v8.dev/blog/math-random for details. npm WARN deprecated chokidar@2.1.8: Chokidar 2 does not receive security updates since 2019. Upgrade to chokidar 3 with 15x fewer dependencies npm WARN deprecated request@2.88.2: request has been deprecated, see https://github.com/request/request/issues/3142 npm WARN deprecated sinon@15.2.0: 16.1.1 added 813 packages, changed 1 package, and audited 816 packages in 30s 116 packages are looking for funding run `npm fund` for detailsWoran könnte das liegen? Berechtigungen? Bin im Docker allerdings als root angemeldet...
Was könnte ich noch versuchen? -
Hallo zusammen, wollte letzte Woche bereits etwas dazu schreiben, aber da es nach dem Fix (erneut) klappte, hab ich die Idee verworfen.
Jetzt habe ich das Problem allerdings wieder. Aber von vorne:
Ich nutze ioBroker auf meiner Synology in der v9-latest.
Anscheinend habe ich im besagten Zeitraum den spotify-premium & telegram-Adapter geupdated, die versagten dann mit 'ERR_INVALID_ARG_VALUE' den Dienst. Dieses Topic war schnell ausfindig gemacht und über die obige Anleitung habe ich die Fixes eingespielt, kontrolliert und alles schien ok zu sein.
Letzte Woche ganbs ein Update der Syno, nach Reboot (der Syno und damit des Containers) standen beide Adapter wieder auf 3.12. Also das Ganze nochmal.
Ich habe jeweils den ioBroker mit "iob maintenance on" beendet, hab unter /opt/iobroker "npm list @iobroker/adapter-core" aufgerufen, bin in die Adapter-Verzeichnisse gewechselt und habe dort "npm i @iobroker/adapter-core@3.1.4". Aufgerufen.
Test mit "npm list @iobroker/adapter-core" sah gut aus (jeweils die 3.14 drauf). Danach den IOB mit "iob maintenance on" wieder gestartet. Ein weiteres "npm list @iobroker/adapter-core" zeigt mir aber jetzt├─┬ iobroker.spotify-premium@1.4.0 │ └── @iobroker/adapter-core@3.1.2 invalid: "^3.1.4" from node_modules/iobroker.spotify-premiumbzw.
iobroker.telegram@3.2.1 │ └── @iobroker/adapter-core@3.1.2 invalid: "^3.1.4" from node_modules/iobroker.telegram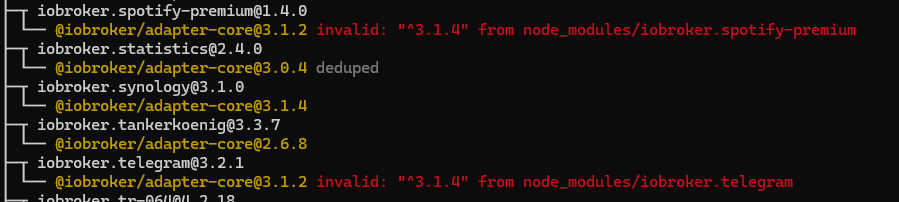
Die Ausgabe nach "npm i @iobroker/adapter-core@3.14" (bei telegram):
npm i @iobroker/adapter-core@3.1.4 sudo: unable to resolve host iobroker-v9-prod: Name or service not known npm WARN deprecated urix@0.1.0: Please see https://github.com/lydell/urix#deprecated npm WARN deprecated har-validator@5.1.5: this library is no longer supported npm WARN deprecated source-map-url@0.4.1: See https://github.com/lydell/source-map-url#deprecated npm WARN deprecated resolve-url@0.2.1: https://github.com/lydell/resolve-url#deprecated npm WARN deprecated source-map-resolve@0.5.3: See https://github.com/lydell/source-map-resolve#deprecated npm WARN deprecated uuid@3.4.0: Please upgrade to version 7 or higher. Older versions may use Math.random() in certain circumstances, which is known to be problematic. See https://v8.dev/blog/math-random for details. npm WARN deprecated chokidar@2.1.8: Chokidar 2 does not receive security updates since 2019. Upgrade to chokidar 3 with 15x fewer dependencies npm WARN deprecated request@2.88.2: request has been deprecated, see https://github.com/request/request/issues/3142 npm WARN deprecated sinon@15.2.0: 16.1.1 added 813 packages, changed 1 package, and audited 816 packages in 30s 116 packages are looking for funding run `npm fund` for detailsWoran könnte das liegen? Berechtigungen? Bin im Docker allerdings als root angemeldet...
Was könnte ich noch versuchen?@manuxi
Versuch maliob fixDa du mit sudo / root unterwegs bist bzw warst (und es dankenswerter Weise gleich sagts - was ev. unnötiges Suchen minimiert - kann es sein, dass die Fileprotections nicht passen. @Thomas-Braun kann da ev. besser helfen - allerdings betet er gefühlter Maßen 24h Tag 'Oh Herr, halt die User von root fern'.
-
@manuxi
Versuch maliob fixDa du mit sudo / root unterwegs bist bzw warst (und es dankenswerter Weise gleich sagts - was ev. unnötiges Suchen minimiert - kann es sein, dass die Fileprotections nicht passen. @Thomas-Braun kann da ev. besser helfen - allerdings betet er gefühlter Maßen 24h Tag 'Oh Herr, halt die User von root fern'.
@mcm57 sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
allerdings betet er gefühlter Maßen 24h Tag 'Oh Herr, halt die User von root fern'.
Mit Recht.
In welchen Verzeichnissen wurden die Befehle ausgeführt?
Das ist beim herumrühren per npm extrem wichtig. Deswegen immer den vollständigen LoginPrompt angeben. -
@mcm57 sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
allerdings betet er gefühlter Maßen 24h Tag 'Oh Herr, halt die User von root fern'.
Mit Recht.
In welchen Verzeichnissen wurden die Befehle ausgeführt?
Das ist beim herumrühren per npm extrem wichtig. Deswegen immer den vollständigen LoginPrompt angeben.@thomas-braun hab unter /opt/iobroker "npm list @iobroker/adapter-core" - dort die beiden Schlingel entdeckt: telegram & spotify-premium. Wie in der Anleitung oben daher in die Verzeichnisse gewechselt:
cd /opt/iobroker/node_modules/iobroker.telegram/
bzw.
cd /opt/iobroker/node_modules/iobroker.spotify-premium/
dort jeweils ein
npm i @iobroker/adapter-core@3.1.4
ausgeführt.
Danach gecheckt:
cd /opt/iobroker/
"npm list @iobroker/adapter-core"- alles gut.
Nach reboot des Containers wieder alles krumm. Vermutlich Permissions :(
-
@thomas-braun hab unter /opt/iobroker "npm list @iobroker/adapter-core" - dort die beiden Schlingel entdeckt: telegram & spotify-premium. Wie in der Anleitung oben daher in die Verzeichnisse gewechselt:
cd /opt/iobroker/node_modules/iobroker.telegram/
bzw.
cd /opt/iobroker/node_modules/iobroker.spotify-premium/
dort jeweils ein
npm i @iobroker/adapter-core@3.1.4
ausgeführt.
Danach gecheckt:
cd /opt/iobroker/
"npm list @iobroker/adapter-core"- alles gut.
Nach reboot des Containers wieder alles krumm. Vermutlich Permissions :(
@manuxi hast du mal ein
iob fixgefahren? -
@thomas-braun hab unter /opt/iobroker "npm list @iobroker/adapter-core" - dort die beiden Schlingel entdeckt: telegram & spotify-premium. Wie in der Anleitung oben daher in die Verzeichnisse gewechselt:
cd /opt/iobroker/node_modules/iobroker.telegram/
bzw.
cd /opt/iobroker/node_modules/iobroker.spotify-premium/
dort jeweils ein
npm i @iobroker/adapter-core@3.1.4
ausgeführt.
Danach gecheckt:
cd /opt/iobroker/
"npm list @iobroker/adapter-core"- alles gut.
Nach reboot des Containers wieder alles krumm. Vermutlich Permissions :(
Zeig mal konkret die vollständigen Ein- und Ausgaben aus der Konsole (in CodeTags eingebettet), keine freien Nacherzählungen.
-
@manuxi sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
@homoran nein. ist das sinnvoll?
Natürlich!
@manuxi sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
Vermutlich Permissions
die würden dadurch gefixt
-
Zeig mal konkret die vollständigen Ein- und Ausgaben aus der Konsole (in CodeTags eingebettet), keine freien Nacherzählungen.
@thomas-braun sagte in Lösung für Fehler: TypeError [ERR_INVALID_ARG_VALUE]:
Zeig mal konkret die vollständigen Ein- und Ausgaben aus der Konsole (in CodeTags eingebettet), keine freien Nacherzählungen.
Gerade schwierig, da keinen ssh-Zugriff. Aber die beiden scheinen gerade auch wieder zu Laufen. Mal schauen, was anch dem nächsten Reboot passiert.
Hey! Du scheinst an dieser Unterhaltung interessiert zu sein, hast aber noch kein Konto.
Hast du es satt, bei jedem Besuch durch die gleichen Beiträge zu scrollen? Wenn du dich für ein Konto anmeldest, kommst du immer genau dorthin zurück, wo du zuvor warst, und kannst dich über neue Antworten benachrichtigen lassen (entweder per E-Mail oder Push-Benachrichtigung). Du kannst auch Lesezeichen speichern und Beiträge positiv bewerten, um anderen Community-Mitgliedern deine Wertschätzung zu zeigen.
Mit deinem Input könnte dieser Beitrag noch besser werden 💗
Registrieren Anmelden
